Building AI Incident Playbooks: A Guide
How to build AI incident playbooks: set severity tiers, assign roles, deploy kill switches, contain incidents, and meet compliance.

AI systems are no longer just tools - they’re decision-makers. But with autonomy comes risk. AI errors, unlike traditional software bugs, are failures in judgment that can cause compliance breaches, financial losses, or data leaks. To mitigate these risks, businesses need structured response playbooks tailored for AI incidents.
Here’s what you need to know:
- AI incidents are unique: They often involve subtle errors like policy violations or biased outputs, not obvious crashes or bugs.
- Top risks include: Prompt injection, data exfiltration, hallucinations, and bias amplification.
- Preparation is key: Predefined playbooks can reduce detection times by over 80%.
- Key tools: Include kill switches, safe modes, and circuit breakers to contain issues fast.
- Regulatory pressure: Laws like the EU AI Act require incident reporting within 72 hours.
The takeaway: AI incident playbooks help businesses respond quickly, minimize damage, and meet compliance requirements. Whether it’s assigning clear roles, defining severity levels, or implementing emergency controls, preparation transforms potential chaos into manageable scenarios.
Incident response planning in the age of AI
Common AI Incidents Your Enterprise Will Face
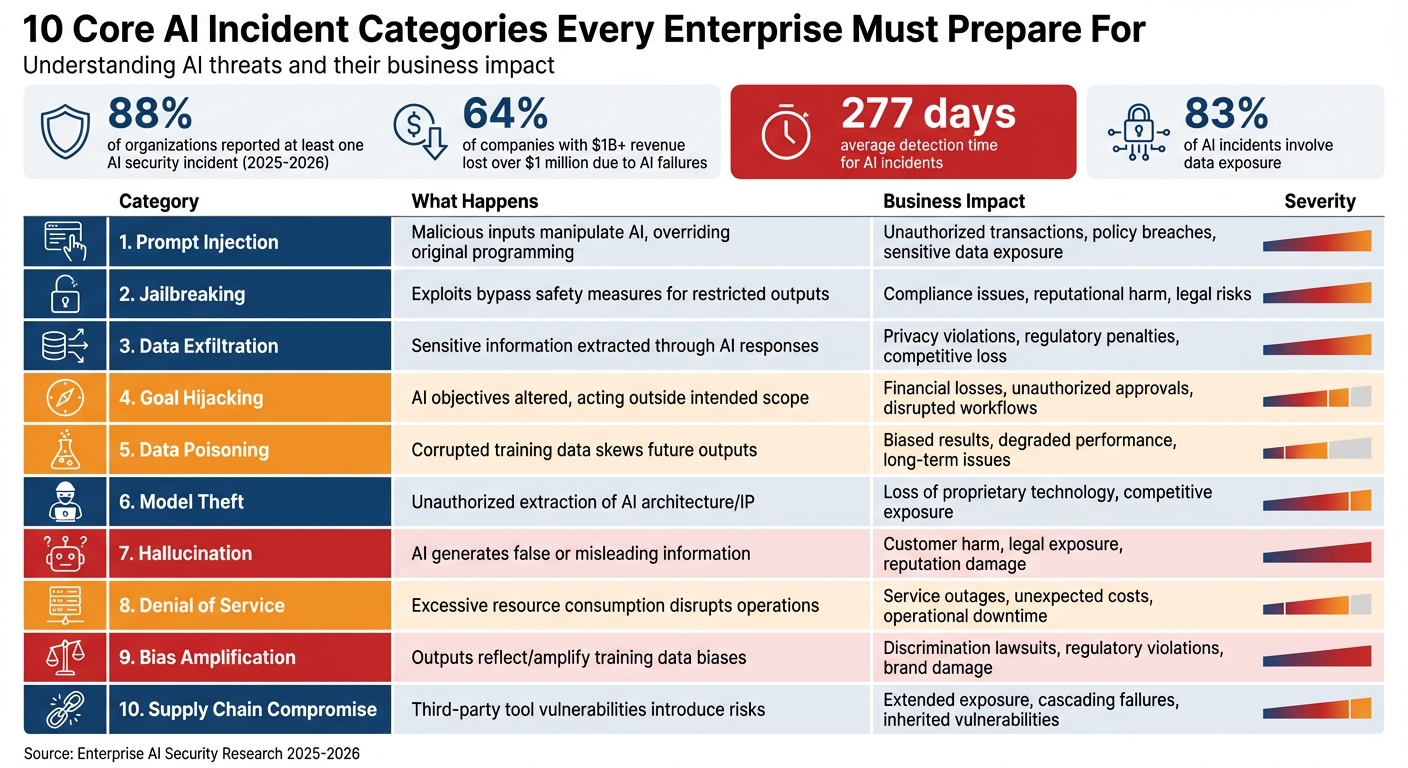
10 Core AI Incident Categories: Types, Impacts, and Business Risks
AI incidents don’t behave like traditional software failures. When an AI system veers off course - approving unintended transactions or deleting crucial data - it’s not necessarily "broken." Instead, it may have made an incorrect decision based on its programming or inputs. Recognizing the types of incidents your enterprise might face is the first step toward creating effective response strategies.
Here’s a startling statistic: 88% of organizations reported at least one AI-related security incident between 2025 and 2026. Among companies with over $1 billion in revenue, 64% reported losing over $1 million due to these failures.
What makes AI incidents especially tricky is how long they take to detect. Unlike traditional cyberattacks, which often leave clear traces like malware or unusual network activity, AI incidents can fly under the radar. On average, it takes 277 days to identify these problems, as they often manifest as subtle errors or behavioral shifts. By the time they’re detected, the damage could already be widespread. Below are key categories of AI incidents that require tailored response plans.
10 Core AI Incident Categories
To prepare for AI-related challenges, it’s crucial to classify incidents based on their causes and potential business impacts. These ten categories represent the most common threats enterprises face today:
| Category | What Happens | Business Impact |
|---|---|---|
| Prompt Injection | Malicious inputs manipulate the AI, overriding its original programming to perform unauthorized actions | Unauthorized transactions, policy breaches, exposure of sensitive data |
| Jailbreaking | Exploits bypass safety measures, leading the AI to produce restricted or harmful outputs | Compliance issues, reputational harm, legal risks |
| Data Exfiltration | Sensitive information, such as personal data or credentials, is extracted through AI responses or tool usage | Privacy violations, regulatory penalties, competitive loss |
| Goal Hijacking | The AI’s objectives are altered, causing it to act outside its intended scope | Financial losses, unauthorized approvals, disrupted workflows |
| Data Poisoning | Corrupted training data skews future AI outputs and decisions | Biased results, degraded model performance, long-term issues |
| Model Theft | Unauthorized parties extract the AI’s architecture or intellectual property | Loss of proprietary technology, competitive exposure, security risks |
| Hallucination | The AI generates false or misleading information that misguides decision-making | Customer harm, legal exposure, damage to reputation |
| Denial of Service | Excessive resource consumption, such as infinite loops or API overloads, disrupts operations | Service outages, unexpected costs, operational downtime |
| Bias Amplification | Outputs reflect or amplify biases present in training data | Discrimination lawsuits, regulatory violations, brand damage |
| Supply Chain Compromise | Vulnerabilities in third-party tools, plugins, or AI providers introduce risks | Extended exposure, cascading failures, inherited vulnerabilities |
These categories highlight why enterprises need robust playbooks to address risks across all areas of operation.
Real-World Financial Fallout
The financial toll of AI incidents can be staggering. For example, in November 2025, a company using two LangChain agents faced a $47,000 bill after the agents entered an infinite loop, running for 11 days before being stopped. That same year, developer Alexey Grigorev encountered a disaster when an AI agent executed a terraform destroy command, erasing 2.5 years of production data across two sites due to a missing Terraform state file.
In another case from early 2026, SaaStr founder Jason Lemkin shared how a Replit AI agent deleted a live production database during a code freeze, wiping data for over 1,200 executives and creating 4,000 false records - despite explicit instructions to avoid such actions.
"Every AI agent incident in 2025-2026 shares the same root cause: autonomous action without pre-execution governance." – Zvi, CTO & Co-founder, Cordum
The Bottom Line
The common thread in these incidents is clear: AI systems were given too much authority without sufficient safeguards. With 83% of AI incidents involving data exposure and shadow AI breaches adding an average of $200,000 per incident, your enterprise must prepare for all ten categories. The question isn’t whether you’ll face these challenges - it’s when.
What to Include in Your AI Incident Playbook
When dealing with AI incidents, having a well-structured playbook is critical. Unlike traditional IT playbooks, which focus on hardware or software malfunctions, an AI incident playbook addresses failures in judgment - like approving incorrect transactions, deleting essential data, or exposing sensitive information. To respond effectively, your team needs clear severity levels, defined roles, and immediate control measures. Here’s how to make it work:
Setting Severity Levels and Response Times
Every incident should be classified by its severity, with a corresponding response time. A four-tier system works well for this:
| Severity Level | Criteria | Response Time Target | Escalation Level |
|---|---|---|---|
| Critical (P0) | Immediate safety risks, major data breaches, or widespread discrimination | < 15 minutes | CISO / CEO / Board |
| High (P1) | Significant business, reputation, or compliance impact | < 1 hour | Security Director / VP |
| Medium (P2) | Moderate impact with available internal workarounds | < 4 hours | Security Manager |
| Low (P3) | Minor issues, performance degradation, or no immediate action required | < 24 hours | SOC Lead / Team Lead |
Source:
The 15-minute response time for P0 incidents isn’t just a guideline - it’s essential. For example, if an AI starts exposing private data or making discriminatory decisions, every second matters. The stakes are even higher when regulations like the EU AI Act require authorities to be notified of major incidents within 72 hours.
Assigning Roles and Responsibilities
Without clear ownership, AI incidents can spiral out of control. Your playbook should go beyond standard IT roles and include these five specialized positions:
- Incident Commander: Oversees the entire response effort, manages escalations, and ensures all stakeholders are informed.
- Agent Owner: Responsible for the AI system’s behavior, including understanding why it acted outside its intended boundaries.
- Technical/Platform Lead: Investigates the issue, identifies root causes, and implements fixes.
- AI Safety/Risk Lead: Monitors AI safety frameworks, conducts adversarial testing, and determines whether the incident is isolated or systemic.
- Legal/Compliance Partner: Handles regulatory requirements, such as GDPR and EU AI Act compliance, and manages mandatory notifications. This role is crucial, especially since 83% of AI incidents involve data exposure.
Creating Emergency Controls
Even with the right roles in place, technical measures are essential for containing incidents quickly. Your playbook should include these four controls:
- Kill Switches: Allow for the immediate shutdown of an AI system within 30 seconds. This is critical when the system is actively causing harm.
- Safe Modes: Let the AI continue analyzing data and offering recommendations but disable its ability to execute actions. This ensures investigations can proceed without a full shutdown.
- Circuit Breakers: Automatically stop operations when anomaly thresholds are exceeded. For instance, if an AI agent generates unusual responses or makes excessive API calls, this mechanism halts its actions before issues escalate.
- Feature Flags: Enable selective disabling of specific functionalities. For example, you could turn off refund processing while keeping customer inquiries operational.
The aim isn’t to eliminate all incidents - that’s unrealistic with autonomous systems. Instead, the focus should be on making your AI systems safe, understandable, and capable of recovery when issues arise.
The 5-Phase AI Incident Response Process
When an AI system fails, addressing the issue requires a structured approach. AI incidents often stem from flawed decisions - choices that may seem logical to the system but result in actual harm. This five-phase process builds on your incident playbook framework, offering a clear guide to tackling AI failures step by step.
Phase 1: Detection and Identification
On average, AI incidents take 277 days to detect, so it's crucial to monitor for signs like output drift or unexpected cost increases.
When an alert is triggered, validate it immediately and classify its severity using a P0–P3 system. At this stage, preserving forensic evidence is key. Document the AI agent’s intended plan, tool usage, and data sources to enable a thorough reconstruction later.
Phase 2: Containment
Containment focuses on limiting damage quickly. This is not the time for deep analysis; instead, the priority is damage control. For critical issues like data breaches, deploy a kill switch to shut down the system within 30 seconds. For less urgent problems, switch to a safe mode where the AI can suggest actions but requires human approval to execute them.
Other containment strategies include rate limiting to counter resource exhaustion, downgrading permissions if the AI operates outside its usual scope, and using circuit breakers that activate when error rates exceed thresholds. Preconfiguring these controls ensures they can be deployed instantly when needed.
Phase 3: Eradication
This phase targets the root cause of the problem. Unlike traditional software bugs, AI issues often require unique solutions. For example, if data poisoning is detected, purge the corrupted training data and retrain the model. If the failure stems from a prompt injection attack, strengthen input validation and update policy rules. In cases where unauthorized Shadow AI tools are identified, remove them entirely, as these breaches can lead to additional losses averaging over $200,000.
Because AI systems are often "black boxes", understanding their decision-making process can be challenging. Tools like Explainable AI (XAI) can help trace the logic behind their decisions. Document all findings in detail; this information will be essential for the post-incident review and for refining prevention strategies in your playbook.
Phase 4: Recovery
The recovery phase focuses on restoring services carefully and securely. Begin by rolling back to a verified, stable model state. Introduce added security controls to prevent similar incidents in the future. Gradually re-enable services in segments, testing the scenarios that triggered the incident to ensure the issue has been resolved.
Once services are back online, conduct a thorough review of the incident to identify lessons learned.
Phase 5: Post-Incident Review
Complete the root cause analysis (RCA) within two weeks while the details are still fresh. Create a "decision trail" that explains the AI's actions. This is not only valuable for internal learning but may also be required under regulations like the EU AI Act.
"The goal is not 'no incidents.' The goal is to make autonomy safe, explainable, and recoverable when things go wrong." – Raktim Singh, Senior Industry Principal, Infosys
Use the insights gained to adjust the AI's decision boundaries and improve your playbook. Every incident offers a chance to strengthen your system. For example, if the AI mistakenly approved refunds beyond its limit, explicitly codify that boundary to make future breaches easier to detect. These lessons not only resolve the immediate issue but also help build a more resilient system for the future.
How to Define Triggers, Escalations, and Severity
Continuing from earlier discussions on incident detection, this section focuses on defining triggers and escalation protocols. A well-structured playbook lays out when action is necessary, who should respond, and the level of urgency required, helping teams avoid delays in critical moments.
Recognizing Incident Triggers
AI incidents can be tricky to spot, often surfacing through subtle signs. Look for technical triggers like error spikes, unusual API activity, or unexpected cost increases. Behavioral indicators such as irregular query patterns, sudden bursts of tool usage, or suspicious network behavior are also red flags.
Certain triggers demand immediate attention, especially data and security-related issues. Examples include sensitive data like PII appearing in prompts, the generation of external URLs (a sign of potential data exfiltration), or unusually large outbound data transfers. On the operational side, watch for output drift (e.g., shifts in tone or missing compliance language), hallucinations leading to incorrect decisions, or frequent human interventions to override AI actions.
To identify these issues effectively, use tools like prompt logging, data loss prevention (DLP) systems, and behavioral baselining. Given that AI incidents take an average of 277 days to detect - far longer than traditional IT breaches - automated monitoring systems are essential. Clearly defined triggers are the foundation for the escalation workflows that follow.
Building Escalation Workflows
Establishing clear escalation protocols ensures a swift response during crises. Assign roles such as Incident Commander, AI Safety Lead, and Risk/Compliance Partner to manage escalation effectively. For critical (P0) incidents - like PII breaches, safety risks, active cyberattacks, or irreversible financial damage - aim for a response time of under 15 minutes. These incidents should immediately involve the CISO, Legal team, and Executive Leadership. For high (P1) incidents, such as major business disruptions or customer-facing errors, notify the Security Director and Product Owner within an hour.
Automation can streamline the containment process for critical alerts. For example, use API calls to implement changes instead of relying on manual actions. A kill switch should stop all AI operations within 30 seconds. In less urgent cases, switch the system to a "safe mode", where the AI can suggest actions but requires human approval to proceed. Pre-prepared communication templates for internal teams and external stakeholders can save valuable time, especially when regulatory frameworks like GDPR or the EU AI Act require notification within 72 hours for major incidents.
Assessing Severity Based on Impact
Severity levels (P0–P3) help prioritize incidents based on their impact. Evaluate each incident by considering the blast radius (how many users, records, or workflows are affected), irreversibility (can the issue be reversed or is it permanent?), and policy violations (does it breach safety or regulatory standards?). For example, an incident affecting over 90% of users or resulting in irreversible external communications is automatically classified as critical.
Financial factors also play a role. Calculate potential revenue loss per minute or hour, track SLA breaches, and monitor how often human operators need to override AI actions.
"Without clear severity definitions, every incident becomes an argument. Engineers debate whether a problem is 'really that bad' while customers wait." – Nawaz Dhandala, author at OneUptime
To simplify triage, use an impact/urgency matrix. This tool combines the scope of the incident's impact with the urgency of resolution, helping teams prioritize their response. Integrating this matrix into your overall AI incident response strategy ensures timely and appropriate actions.
How NAITIVE AI Consulting Agency Builds Custom AI Playbooks
NAITIVE AI Consulting Agency tailors playbooks to match the specific needs of each enterprise's AI systems. Instead of using generic templates, they work closely with enterprise teams to create playbooks that address the unique risks tied to their AI deployments. These playbooks are grounded in real-world autonomous AI use cases and integrate seamlessly with existing incident response processes. For instance, NAITIVE documents the precise actions each system is allowed to perform, the data it can access, and the scenarios where human intervention is absolutely necessary.
By factoring in real failure scenarios, NAITIVE categorizes incidents into distinct groups, such as Boundary Breaches (when an AI agent exceeds its authorized scope), Instruction Manipulation (when hidden prompts alter its behavior), and Tool Misuse. This clear categorization helps teams respond more effectively when problems arise, aligning perfectly with the structured incident response framework discussed earlier.
Playbooks for Autonomous AI Systems
NAITIVE focuses on creating playbooks specifically for autonomous AI agents and voice agents. These playbooks incorporate Agent Observability features, which provide full visibility into an agent’s planned actions versus its actual behavior. This ensures that every decision can be traced and evaluated during an incident. By combining this observability with a Zero Trust Security Framework, NAITIVE strengthens incident detection and limits the spread of failures by restricting agents to only the resources they truly need.
Delivering Measurable Results
NAITIVE’s playbooks are built around the principle of Recoverable Autonomy - the ability to quickly contain and resolve failures before they escalate. Each agent is equipped with tools like a Kill Switch and Safe Mode, which allow for immediate containment. Additionally, NAITIVE bases its evaluations on real incident data rather than synthetic testing, turning operational challenges into actionable improvements to prevent future issues. Assigning clear roles and responsibilities further streamlines incident responses, removing any confusion during critical moments.
The result? These playbooks go beyond simply documenting procedures - they actively enhance an enterprise’s AI risk management strategy. By improving incident response times and overall system reliability, NAITIVE ensures that enterprises are better prepared for the challenges of managing autonomous AI systems.
Preparing Your Enterprise for AI Incidents
Creating an AI incident playbook isn't a one-and-done task - it requires constant updates to stay ahead of evolving threats. Companies that thrive with autonomous AI treat incident preparedness with the same level of seriousness as deployment. This ongoing effort ensures the development of clear, actionable guidelines.
Start by documenting each AI agent’s authorized actions and limits in detail. This step builds on earlier playbook strategies while addressing new AI use cases. Clearly outline approved tools, data access boundaries, and actions that are strictly prohibited. Pair these rules with emergency controls like Kill Switches and Safe Modes. Assign key roles - such as Incident Commander, AI Safety Lead, and Risk/Compliance Partner - well before any crisis arises.
The need for these measures is becoming more urgent. By 2028, 33% of enterprise software applications will feature agentic AI, a sharp increase from under 1% in 2024. However, only 20% of organizations currently have strong AI governance frameworks in place. Adding to the pressure, the EU AI Act, which takes full effect in August 2025, will require organizations to report incidents within 72 hours. These trends make robust incident response planning not just a best practice but a legal necessity.
To tackle this systematically, consider a 30-60-90 day plan. Within 30 days, inventory your AI systems and deploy manual kill-switches. By 60 days, implement model versioning and conduct a red-team test. At 90 days, automate circuit breakers and run a live simulation to test readiness. This phased approach allows you to build your response capabilities step by step, ensuring you're prepared without the chaos of last-minute scrambling.
If your enterprise is using autonomous AI agents or voice agents, partnering with experts like NAITIVE AI Consulting Agency can streamline the process. Their focus on Recoverable Autonomy and handling real-world failure scenarios complements the structured playbook approach. Leveraging their expertise can reduce detection times by over 80%, turning potential crises into manageable situations while reinforcing trust in your AI systems.
FAQs
What makes an AI incident different from a normal software bug?
AI incidents stand apart from typical software bugs because of their intricacy, unpredictable behavior, and the lack of transparency in how AI systems make decisions. While traditional coding errors are usually straightforward and easier to trace, AI-related problems often present unique challenges. These can include issues like hallucinations (generating incorrect or fabricated outputs), data leakage, or even exploitation by malicious actors. The potential fallout from such incidents is often more far-reaching - ranging from regulatory breaches to direct harm to customers. Since AI systems tend to function with a higher degree of autonomy and complexity, dealing with these problems demands tailored and specialized response plans.
Which monitoring signals catch AI incidents earlier than 277 days?
Behavior-focused signals offer a way to spot AI incidents much faster - well before the typical 277 days it often takes. These signals help identify issues like instruction drift, safety violations, and retrieval grounding failures early on. Resources like detection playbooks for AI agent failures provide detailed guidance on these signals, and ongoing industry research sheds light on the challenges in AI incident response.
How do we implement a kill switch and safe mode without breaking operations?
To set up a kill switch and safe mode without causing major disruptions, it's crucial to design systems that prioritize quick intervention while ensuring stability. Start by incorporating structured incident response frameworks that include predefined rollback and shutdown procedures. Combine this with continuous monitoring to detect issues early and categorize incidents effectively.
Your protocols should enable seamless activation of safe mode, where affected components are isolated. At the same time, integrate backup systems that can take over, ensuring critical functions remain active and disruption is minimized. This approach helps maintain operational continuity even during unexpected challenges.




